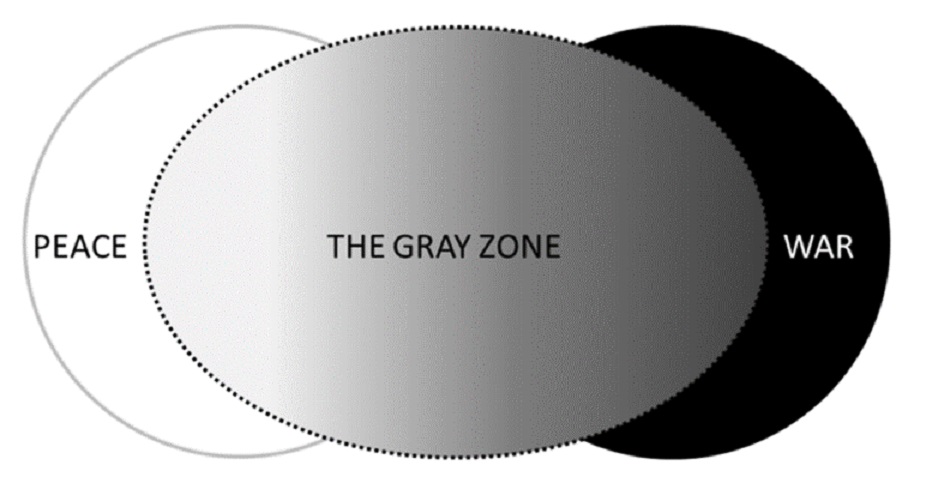
The grey zone between nations are going to increase in the coming years.
A report by Recorded Future in Oct 2020, a Massachusetts-based company, which alleged that a Chinese state-backed entity systematically targeted critical Indian infrastructure installations has brought into sharp focus and turned the spotlight on the grim reality of grey zone battles in recent times. Media reports suggested that the October 2020 power outage in Mumbai and neighbouring areas, which crippled train transportation, closed the stock exchange, and hampered those working from home amidst the pandemic, was sabotage. The power ministry acknowledged that an email was received from CERT-In on 19th November 2020 on the threat of malware called Shadow Pad at some control centres of POSOCO and action has been taken to address these threats. All systems in control centres were scanned and cleaned by antivirus. The incident was investigated by the National Critical Information Infrastructure Protection Centre (NCIIPC), which oversees India’ cybersecurity operations in critical sectors. There is a need to analyse the implication of this new threat, identify vulnerabilities and plug the gaps quickly.
The compulsions of geopolitical competition among rival powers in their need to carve out or expand their areas of influence are increasingly being playing out in the space beyond diplomacy and short of conventional war, which is referred to as the grey zone. The United States Special Operations Command defines grey-zone as “competitive interactions among and within state and non-state actors that fall between the traditional war and peace duality.” A key element of operations within the grey zone is that they remain below the threshold of an attack, which could have a legitimate conventional military response (jus ad Bellum). The concept of the grey zone is not novel and has been often been used in the past as a military strategy in proxy wars, low-intensity conflicts and sponsoring non-state players. Although it reflects an age-old approach, however, in recent times the advances in information technology and our growing dependence on IT have created vulnerabilities that are now being targeted by the adversary. Cyber-attacks, fake news, disinformation, subversion of democratic institutions and destroying social cohesion are the new norm in this grey zone battlefield and is being increasingly used to create new and radical spaces for its expansion.
Nathan Freier, an associate professor of national security studies at the U.S. Army War College’s Strategic Studies Institute, in his article “The Darker Shade of Gray: A New War Unlike Any Other”, suggests that all grey zone strategies include unique combinations of hostile methods within and across instruments of power, traditional domains (air, land, sea, space, cyber), and heavily contested competitive spaces (e.g., electro-magnetic spectrum and strategic influence). He also emphasises that grey zone adversaries present a menace to the convention, in that the character of their competitive methods promises warlike outcomes yet fall short of military provocation and concludes that rival grey zone strategies and approaches “lie between ‘classic’ war and peace, legitimate and illegitimate motives and methods, universal conditions and norms, order and anarchy.”
While the toolkit for grey zone operations includes information operations, political coercion, economic coercion, cyber operations, proxy support, and provocation by state-controlled forces, this article examines the dimension of cyber operations with specific reference to the vulnerability of critical infrastructure principally power grids to cyber-attacks.
With the increasing dependence on IT, the power generation and distribution network system face new and evolving cybersecurity threats. One of the first publicly acknowledged cyberattack to have caused a grid power outage was in 2015, on distribution utility substations in Ukraine, which shut off power to over 225,000 utility customers for several hours. The cyber attackers are reported to have used the BlackEnergy 2 malware to cause the grid failure. The second cyberattack in Ukraine in 2016 was reported on an electricity control centre in the city of Kyiv, shutting down substations, which controlled 200 megawatts of capacity using the malware named “Industroyer” or “Crash Override”. This was reported to be the second known malware specifically designed to disrupt physical systems. The first malware recognized as targeting SCADA (supervisory control and data acquisition) systems was the STUXNET computer worm, which was reported in 2010 to have destroyed centrifuges for uranium enrichment in Iran.
The US Congressional Research Service report in 2018, on Electric Grid Cybersecurity5, highlights the vulnerabilities in the system which are summarised below.
Cyber threats could result in direct attacks aimed at the electric grid or other critical infrastructure that could impact the operations or security of the grid. Cyber intrusions on the electric grid have resulted in malware on ICS networks with the capability of causing damage or taking over certain aspects of system control or functionality.
One of the greatest cyber threats to the grid is intrusions focused on manipulating Industrial Control System (ICS) networks. According to the Report, in 2017, the security firm Dragos (which specializes in industrial control systems) found 163 new security vulnerabilities in industrial control devices, which is classified as typically “insecure-by-design,” since they were located deep within ICS networks. It found that 61% of these vulnerabilities would likely cause a “severe operational impact” if exploited in a cyberattack.
Operational Technology OT systems are often used by electric utilities to monitor and control power production processes. While these technologies have been considered air-gapped (i.e., separate from IT systems), the modernization of ICS networks has led to OT and IT systems becoming increasingly interconnected. While a lot of attention has been focused on IT system cybersecurity, this is not always the case for OT networks. OT systems are often directly connected to the Internet, in some cases so that third-party vendors can remotely connect to the system to perform diagnostics and maintenance. In many of these instances, the OT systems are not protected by a firewall and are outdated, so they lack modern security features that would typically be used to protect an internet-facing connection (e.g. multi-factor authentication, strong passwords, logging, and monitoring)
The human factor is considered by many to be the weakest link in cybersecurity. Many cybersecurity breaches are caused by individuals falling prey to phishing or similar attacks which are used to gain credentials to access utility systems. This was the case in Ukraine, as hackers sent out malware-carrying emails. After links in the emails were opened by legitimate users, hackers acquired the credentials needed to access control and operations systems to cause blackouts at regional distribution utilities. The report highlights that the targeted phishing attacks are on the rise against electric utilities in the U.S., Europe, and parts of East Asia with spear-phishing attacks that employ code and infrastructure eerily similar to that used by the so-called Lazarus Group (North Korea based hacking group), the most destructive and outright criminal of the state-sponsored hacking gangs.
With this as a background, let us examine the power outage in Mumbai and try and connect the dots.
Electricity generation and distribution are vital to the commerce and daily functioning of any nation. The National Grid is the high-voltage electricity transmission network in India, connecting power stations and major substations and ensuring that electricity generated anywhere in India can be used to satisfy demand elsewhere. The National Grid is owned and maintained by the state-owned Power Grid Corporation of India and operated by the state-owned Power System Operation Corporation. It is one of the largest operating synchronous grids in the world with 371.054 GW of installed power generation capacity as of 30 June 2020. The system is operating through five regional grids, Northern, Eastern, Western, North-eastern, and Southern grids connected synchronously.
Therefore, power grids constitute a prime target for Grey Zone tactics, as it could cause huge financial losses. This is borne out by the fact that this is not the first time India’s critical infrastructure has been in the crosshairs of cyber attackers. Some other high-profile cyberattacks on India’ power sector include the ones at state-run Nuclear Power Corp. of India Ltd.’s (NPCIL) Kudankulam Nuclear Power Plant (KKNPP), THDC Ltd.’s Tehri dam, West Bengal State Electricity Distribution Co. Ltd, and at Rajasthan and Haryana discoms.
The Recorded Future report explains the details of the attacks against the Indian power sector. It identified the activity through a combination of large-scale automated network traffic analytics and expert analysis. What is germane is that the intrusion activity was undertaken using the PlugX malware C2 infrastructure in the digital space against multiple Indian governments, the public sector, and defence organizations from at least May 2020. This PlugX intrusion activity gained momentum after the Indian and Chinese troops faced off on May 20. These were allegedly carried out by RedEcho, a Chinese state-sponsored Threat Actor Group, which allegedly penetrated a total of 12 organizations, including four of India’s five Regional Load Despatch Centres (RLDCs) and two State Load Despatch Centres (SLDCs). These organizations are responsible for ensuring the optimum scheduling and dispatching of electricity based on supply and demand across regions in India. According to Recorded Future, “The targeting of Indian critical infrastructure offers limited economic espionage opportunities; however, we assess they pose significant concerns over potential pre-positioning of network access to support Chinese strategic objectives.”
The energy sector was targeted using ShadowPad, a modular backdoor that has been in use since 2017. ShadowPad is shared among other state-backed threat actor groups who are affiliated with both the Chinese Ministry of State Security (MSS) and the People’s Liberation Army (PLA). Some of these groups include APT41 (aka Barium, among others), Icefog, KeyBoy (aka Pirate Panda), Tick, and Tonto Team. There is no doubt that the timing of these alleged attacks through sponsored groups lends credence that grey zone warfare will increasingly target power grids, which are susceptible to cyber intrusions.
Even as we try to come to terms with dealing with cyber-attacks on grids, advances in technology have revolutionised how devices interconnect on the internet. IoT (Internet of Things) is the concept of connecting any device (so long as it has an on/off switch) to the Internet and to other connected devices, which results in a giant network of connected devices. This has raised new concerns about the vulnerability of networks, as IoT devices have been increasingly targeted by botnet malware (whereby the hacker takes over the operation of a large number of infected devices) to launch denial-of-service or other cyberattacks. If such IoT cyberattacks were able to access electric utility ICS networks, they could potentially impair these systems or cause electric power networks to operate based on manipulated conditions or false information. For example, a potential IoT-based attack on residential or commercial thermostats could result in false power demand readings, causing a utility to ramp up power production unnecessarily.
In conclusion, there is no doubt that in the future more such battles will be fought in the Grey Zone as they remain below the threshold of an attack, which could have a legitimate conventional military response. The zone beyond diplomacy and short of conventional war offers disproportionately large dividends compared to investments required in conventional battles. These battles are invariably played out by state-backed threat actor groups who have clandestine links with government agencies. The toolkit for grey zone operations is constantly being evolved as new vulnerabilities are discovered. Fake news, disinformation, subversion of democratic institutions and destroying social cohesion are already being used as tools of warfare in this grey zone battlefield by rival powers try to settle scores. Cyber operations and Cyber-attacks against Critical Information Infrastructure Organisations (both public and private) is a reality now. Power grids are critical infrastructure and will be a prime target for Grey Zone tactics, as their breakdowns could cause huge financial losses. The need to safeguard them is essential, as they are the backbone to the economic development and growth of a nation.
Disclaimer: The views and opinions expressed by the author do not necessarily reflect the views of the Government of India and Defence Research and Studies
Title image courtesy: https://www.realcleardefense.com/articles/2020/12/07/between_peace_and_war_gray_zone_bright_line_or_dialectic_652193.html
References:
1. Recorded Future is a privately held cybersecurity company founded in 2009 with headquarters in Somerville, Massachusetts. The company specializes in the collection, processing, analysis, and dissemination of threat intelligence by the use of patented machine learning and natural language processing methods to continuously collect and organize data from the open web, dark web, and technical sources. Its recent report details the campaign conducted by a China-linked threat activity group RedEcho targeting the Indian power sector. The report can be accessed at https://www.recordedfuture.com/redecho-targeting-indian-power-sector/
2. On 12 October 2020 power outage in Mumbai and neighboring areas, crippled train transportation, closed the stock exchange, and brought Mumbai to a standstill.
3. Kapusta, Philip. “The Gray Zone” (https://www.soc.mil/SWCS/SWmag/archive/SW2804/GrayZone.pdf) (PDF). www.soc.mil. United States Special Operations Command.
4 . Electricity Information Sharing and Analysis Center, Analysis of the Cyber Attack on the Ukrainian Power Grid,
March 18, 2016,
https://www.nerc.com/pa/CI/ESISAC/Documents/E-ISAC_SANS_Ukraine_DUC_18Mar2016.pdf.
5. Electric Grid Cybersecurity Updated September 4, 2018, Congressional Research Service, https://crsreports.congress.gov R45312
6 SCADA is supervisory control and data acquisition system which gathers information from remote stations across a utility system to control geographically dispersed assets.
7. David Kushner, The Real Story of Stuxnet, IEEE, February 26, p. 2013, https://spectrum.ieee.org/telecom/security/the-real-story-of-stuxnet
8. ICS comprises electronic devices, switches, and circuit breakers to regulate and report on the flow of electricity at different parts of the system and help to manage & control power plant, transformer yard and power bus functions, transmission, and distribution substations. Today, widely available software applications and Internet-based devices have been deployed into most ICS, delivering effective and efficient outcomes, but also increasing system vulnerability.
9. “Areas of national grid”. Retrieved 19 October 2016. http://www.iexindia.com/bidareas.aspx?id=31&mid=2
10. “All India Installed Capacity of Utility Power Stations” (PDF). Retrieved 10 July 2020. http://cea.nic.in/reports/monthly/installedcapacity/2020/installed_capacity-06.pdf
12. A 2015 report from the University of Cambridge and Lloyds of London, estimates that a targeted cyberattack could leave 15 states and 93 million people from New York City to Washington, DC, without power. The scenario estimated the total impact to the U.S. economy at between $243 billion and $1 trillion, resulting from “direct damage to assets and infrastructure, decline in sales revenue to electricity supply companies, loss of sales revenue to business and disruption to the supply chain”. http://www.nap.edu/ catalog/12050/terrorism-and-the-electric-power-delivery-system
14. The PlugX malware family is well known to researchers, with samples dating back to as early as 2008, according to researchers at Trend Micro. PlugX is a fully-featured Remote Access Tool/Trojan (RAT) with capabilities such as file upload, download, and modification, keystroke logging, webcam control, and access to a remote cmd.exe shell. For a detailed account of how PlugX works see https://logrhythm.com/blog/deep-dive-into-plugx-malware/